Configure a Vulnerability Feed
Use your favorite vulnerability scanner to drive team security action
FortMesa is built to make Vulnerability Management a team-sport that includes security professionals, technologists, and business stakeholders each participating in their own specific way.
Before getting the full team involved it will be necessary to configure an external vulnerability source.
Choosing a vulnerability source
If you're using Amazon Web Services (AWS) you're in luck because AWS has a great built in vulnerability tool called Inspector. Adding a FortMesa Trust will allow FortMesa to scan for and download vulnerability data AWS can collect from your systems.
Add a FortMesa Trust to Your AWS Account
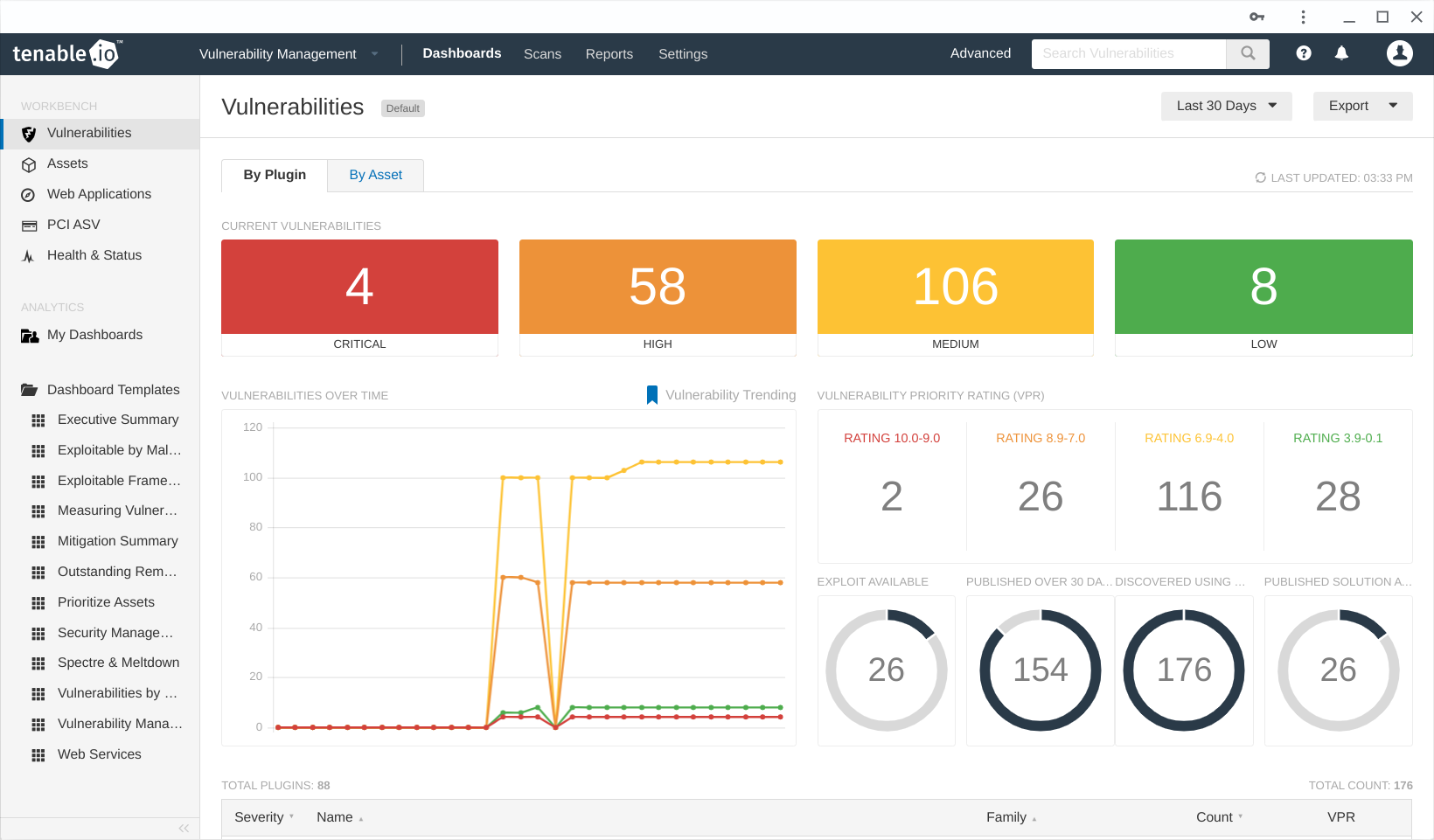
If you're looking for a comprehensive solution FortMesa works great with Tenable.io contact FortMesa support to assist with the connection.
- Finds vulnerabilities on-prem or in the cloud
- Agent-based scanning on Windows, MacOS and Linux
- Authenticated or unauthenticated network scanning
- Scans inside containers and across external web surfaces
- Supports PCI-DSS as an Approved Scanning Vendor (ASV)
If you are limited to free or freemium open-source solutions you may want to consider Nexpose, Metasploit or OpenVAS. These or any other structured vulnerability feed (such as 'npm audit') can be configured using our open source SDK and integration kit.
Discover Vulnerabilities
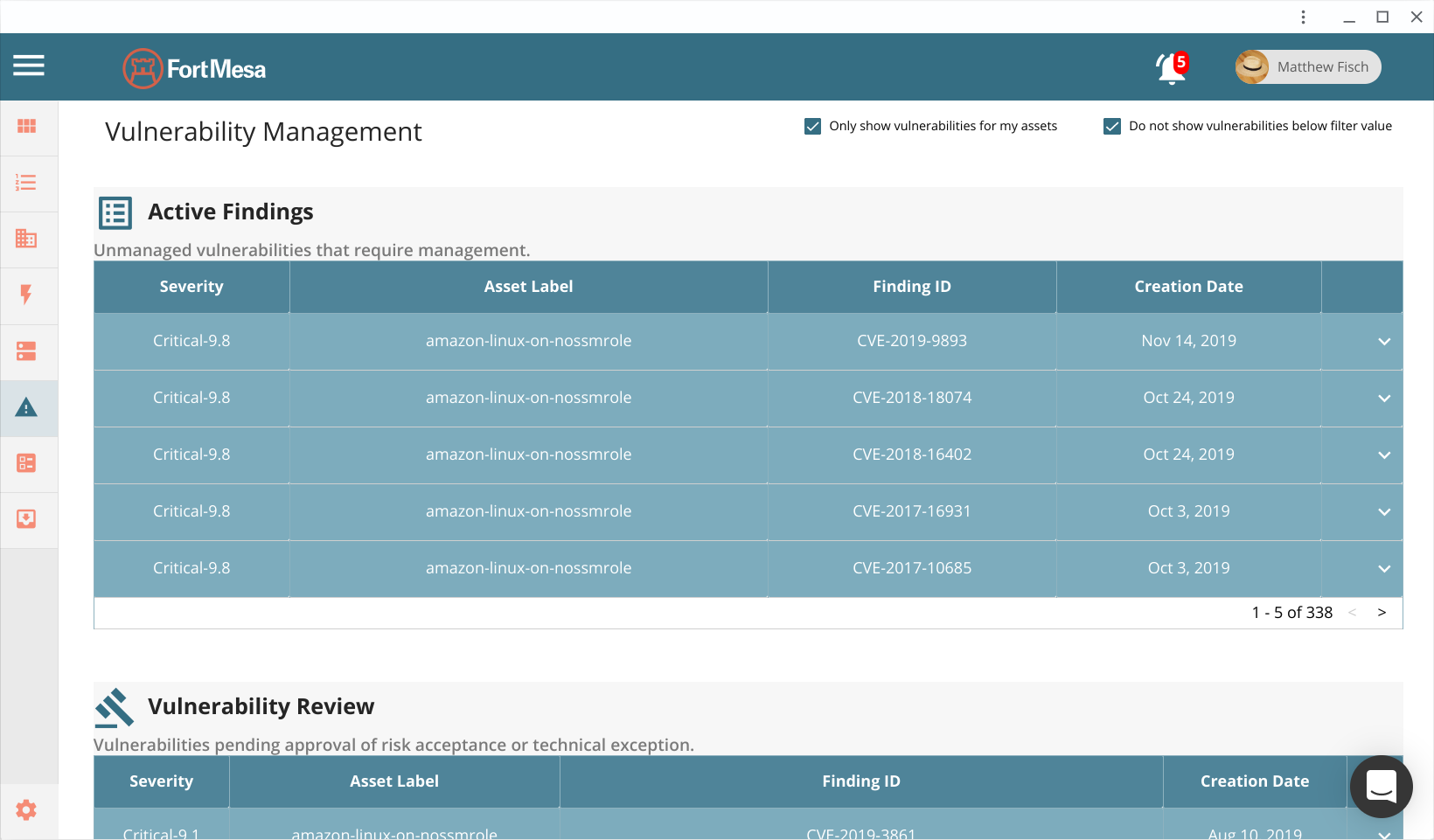
Try toggling the "Only show vulnerabilities for my assets" box to make sure you're seeing everything. After your first scan is collected by FortMesa you will almost always find vulnerabilities. Security is hard.
Set Severity Filters
Because the vulnerability list can be long we've made it easier to focus on the most important security actions. Review the "Vulnerability Management" settings screen to set filters right for you. By default no vulnerabilities are filtered.
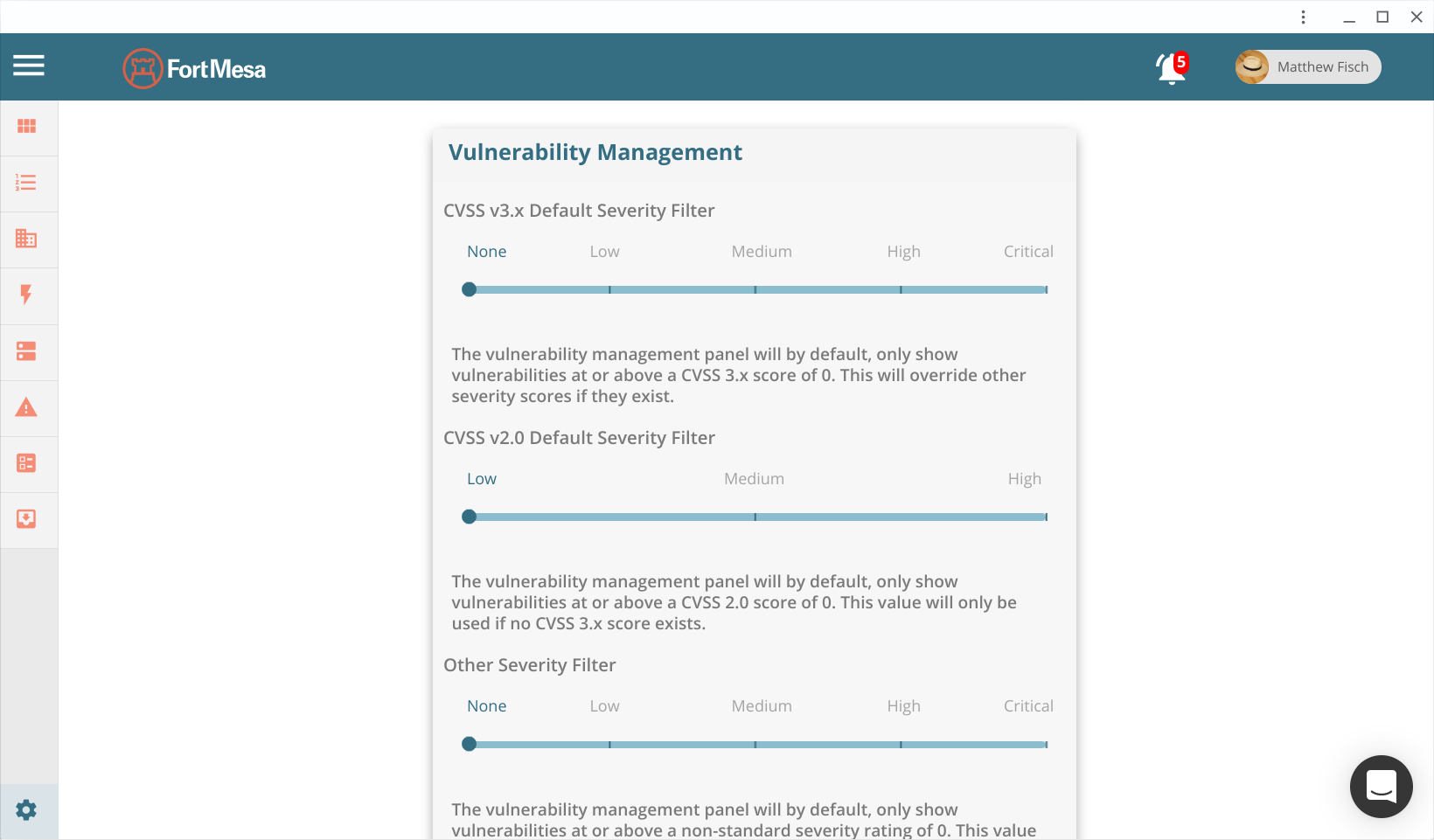
Set the filters right for your organization and click save. You may consider starting at a high threshold and slowly moving toward a lower one as your security posturing improves.
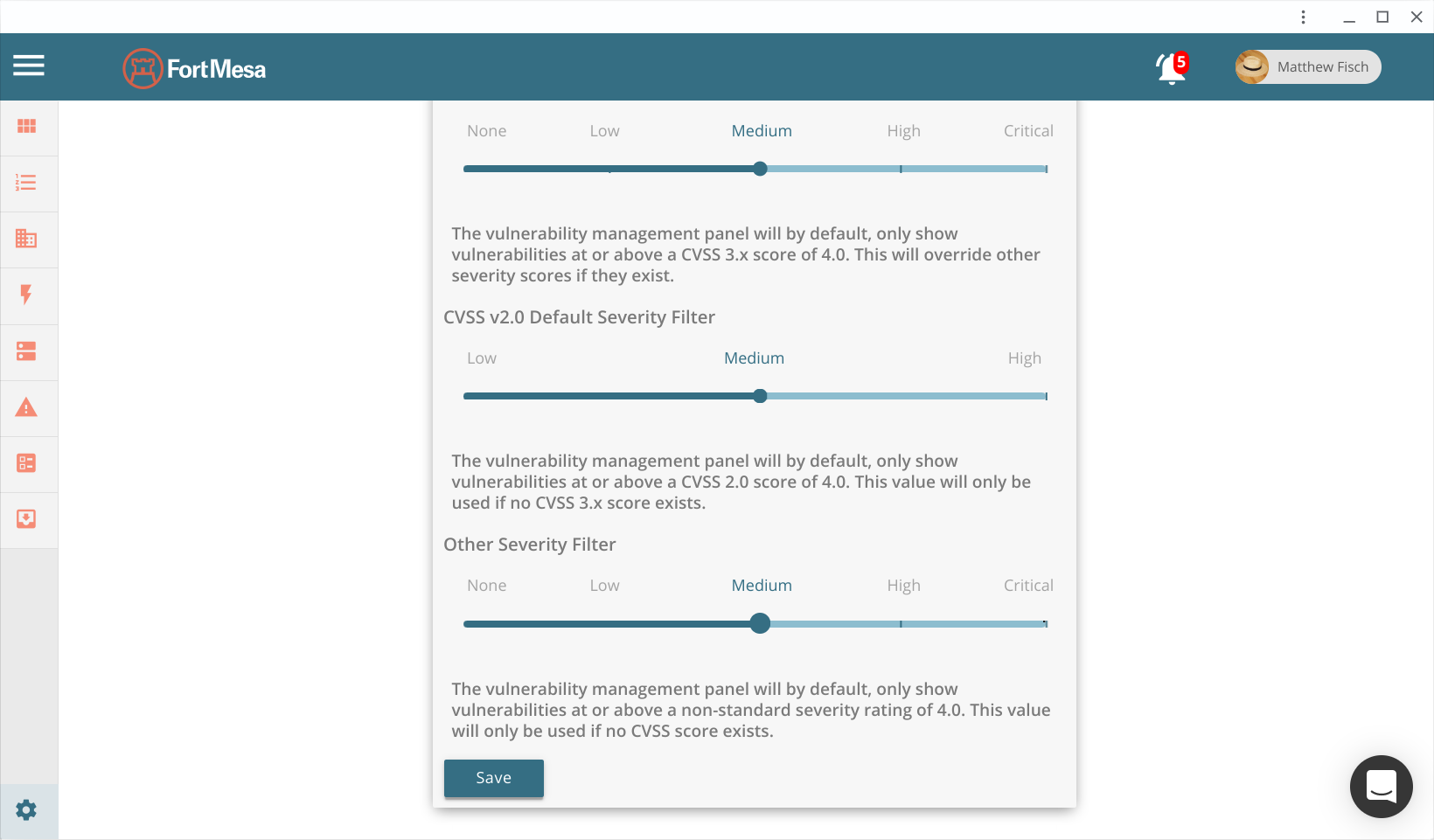
Your vulnerability list will now default to excluding vulnerabilities below your set filter. This will also affect notifications and priority tasking. Keep in mind, you can always uncheck the "Do not show vulnerabilities below filter value" box in the vulnerability management pane to preview vulnerabilities with a lower score.
Manage Vulnerabilities
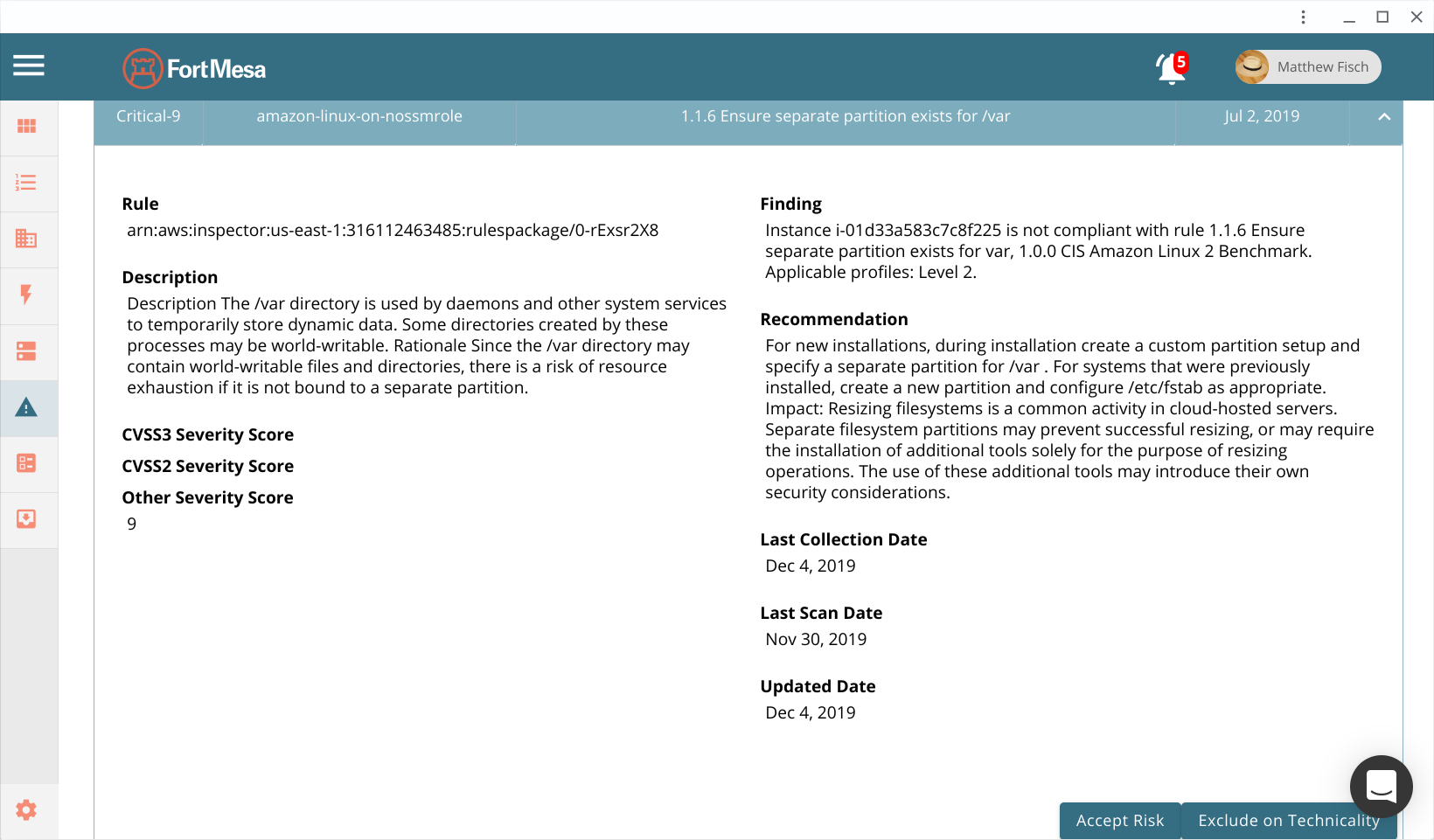
Vulnerabilities can be created by any number of technical issues, the methods of management however have only a few categories of solution.
Remediate a vulnerability by fixing the problem
The best solution is usually to remediate the underlying technical issue. Often times this is as simple as tweaking a setting or applying a vendor software patch or upgrade. When this happens FortMesa will automatically remove the vulnerability from Active status after the next vulnerability scan.
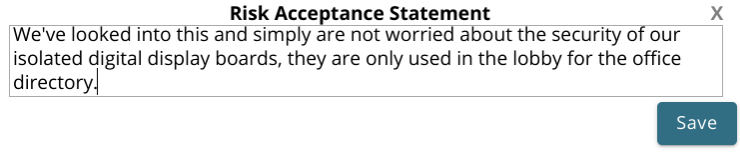
Accept the risk posed by a vulnerability
Sometimes the vulnerability cannot be easily remediated. If the fix is not economically justified the Asset Owner can document their acceptance of the risk.
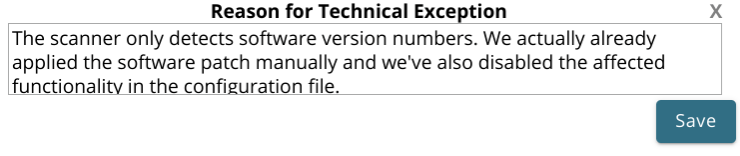
Exclude a vulnerability from the list based on a technicality
False positives do occur, and in these cases an Asset Custodian may log a rare exception. These should never be used if a technician simply disagrees with the risk (instead, tell the asset owner!).
Vulnerability review
If a vulnerability is managed using a risk acceptance or technical exception workflow it will still be listed in the vulnerability management pane.
Multi-stakeholder accountability is the cornerstone of a well functioning security program. After an Asset Owner or Asset Custodian logs risk acceptance an accountable security professional needs to review, then Approve or Deny the stakeholder submitted notation.
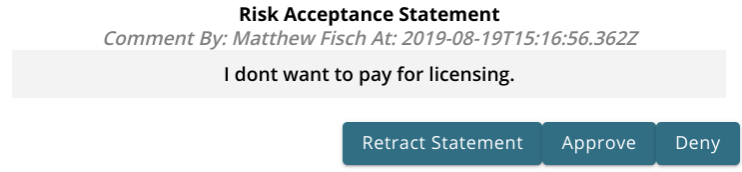
Only FortMesa users designated the "Information Security Engineer" can perform this task. The security professional's job is not to second guess the decisions of another person. The primary importance here is to make sure the technician or business stakeholders responsible for logging a vulnerability management notation are sufficiently informed.
If your organization has no security professionals on staff, your designated Information Security Officer can fulfill this function as a simple dual-party control.

